As security breaches continued to grab headlines over 2014, I was intrigued by new claims that not only could online security be improved for consumers, but it could actually become a more delightful user experience. The launch of Apple Pay has proven to us that this is possible.
With over 150 FIDO members, the Board of Directors alone reads like a Who’s Who List: Alibaba/Alipay, ARM, Bank of America, CrucialTec, Discover Financial Services, Google, Identity X, Lenovo, MasterCard, Microsoft, Nok Nok Labs, NXP semiconductors, Oberthur Technologies, PayPal, Qualcomm, RSA Security, Samsung, Synaptics, Visa, and Yubico.
Keen to understand what attracted so many key players, I was delighted to have an opportunity to interview Executive Director of the FIDO Alliance, Brett McDowell, to understand more about how all this works and what changes we are likely to see in the world of payments because of this.
Brett, I’ve heard so much about FIDO as the standard behind high profile launches of 2014, and am keen to understand more. Could you share a bit about yourself and your mission at FIDO?
I am currently the Executive Director of the FIDO (Fast IDentity Online) Alliance which I helped to found in July 2012, when I was the Head of Ecosystem Security at PayPal, to address the lack of interoperability among strong authentication devices as well as the problems users face with creating and remembering multiple usernames and passwords. At the FIDO Alliance, we are changing the nature of online authentication by developing specifications that define an open, scalable, interoperable set of mechanisms that supplant reliance on passwords to securely authenticate users of online and mobile services.
Previously I spent several years at PayPal where, as Head of Ecosystem Security, I was tasked with developing strategies and leading initiatives to make the Internet a safer environment for PayPal and its customers. I spearheaded authentication strategy, including working with global policy makers to evolve best practices in strong authentication regulation. Prior to joining PayPal I spent several years as Executive Director of industry standards organizations, including Liberty Alliance and Kantara Initiative, which produced standards and accreditation programs in the field of digital identity.
At the FIDO Alliance, our mission is tightly scoped to producing open standards and industry adoption programs that enable implementers to change the nature of online authentication by improving user experience while simultaneously providing better security in a very privacy-respecting manner. We just released the final FIDO 1.0 specifications at the end of 2014.
Why did you feel standards were needed relating to strong authentication, and how does this differ from traditional authentication?
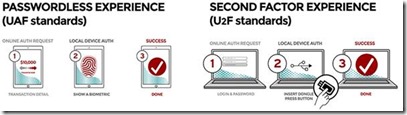 So, “traditional” is an interesting word in the context of strong authentication, as the concept has not gotten a tremendous amount of adoption, especially not from consumers. Before FIDO authentication, if you were an online service provider, in order to authenticate your users, you would typically use username and password. If you wanted more security you had to add another authentication factor from a set of options that were not necessarily designed for ease-of-use. The “historic” approach to multi-factor authentication, or “strong authentication” as it is often called, combines “something you know” (like a password or other form of “shared secret”) with another factor, such as “something you are” (a biometric for instance) or “something you have” (such as a token or physical device). The industry norm in 2011-2012, before FIDO authentication was announced, was username and password as the ubiquitous first-factor, and the second factor, if there was one, was typically a 6-digit one-time-use passcode. You’d get the second factor through an SMS to your mobile device or create it on a specialised hardware device or copy it from a code-generating mobile app on your smartphone. This 6 digit number- the one-time password (OTP) - is called a security token.
So, “traditional” is an interesting word in the context of strong authentication, as the concept has not gotten a tremendous amount of adoption, especially not from consumers. Before FIDO authentication, if you were an online service provider, in order to authenticate your users, you would typically use username and password. If you wanted more security you had to add another authentication factor from a set of options that were not necessarily designed for ease-of-use. The “historic” approach to multi-factor authentication, or “strong authentication” as it is often called, combines “something you know” (like a password or other form of “shared secret”) with another factor, such as “something you are” (a biometric for instance) or “something you have” (such as a token or physical device). The industry norm in 2011-2012, before FIDO authentication was announced, was username and password as the ubiquitous first-factor, and the second factor, if there was one, was typically a 6-digit one-time-use passcode. You’d get the second factor through an SMS to your mobile device or create it on a specialised hardware device or copy it from a code-generating mobile app on your smartphone. This 6 digit number- the one-time password (OTP) - is called a security token.
The first problem with OTP -- and one of the many issues that FIDO authentication inherently addresses -- is usability. The first word in FIDO is fast, and it helps to explain why FIDO technologies became so disruptive so quickly. We are not about bolting on extra security that puts the burden on the user. We are about delivering an end-to-end innovative approach to authentication through a new, open, online cryptographic protocol that enables best-of-breed device-centric authentication to be used for online access.
How does the FIDO UAF Architecture enable online services and websites to leverage native security features of devices and what problem does this address?
From the payments perspective our standards enable a better user experience – faster, more secure, privacy respecting and easier-to-use. An example is, Samsung has enabled a number of payments applications using FIDO to allow a user to simply swipe a finger across a sensor on their smartphone or tablet. This is arguably easier than everything else in the market, certainly easier than passwords.
Although the concept of strong authentication has been around for a while and pretty well adopted by pockets of the enterprise market, it has not achieved widespread adoption beyond the enterprise because it has lacked the means to achieve interoperability among systems and devices; FIDO authentication standards enable any strong authentication method, what we call “authenticators”, to interoperate with any online service, independent of solution vendor or device.
Without interoperable strong authentication, you are left with the classic “token necklace” problem; wearing specialized security tokens, often around your neck with your security badge at work, for each online service that requires strong authentication because you cannot use any one of them to authentication into the other online applications. This is because “traditional” strong authentication relied on proprietary centralized servers (closed systems) connecting authenticators in the hands of users to proprietary server side functionality. Limited in both reach and function, strong authentication solutions have been neither open nor interoperable, until FIDO UAF and U2F 1.0 standards , which have opened the door for ubiquitous strong authentication through “net effects” that only emerge from an open ecosystem.
Is this interoperability issue something you address through UAF and U2F?
Yes, both UAF and U2F protocols, applied to devices, client software and online servers, produce entirely interoperable strong authentication. What the FIDO Alliance founders introduced first was the Universal Authentication Framework (UAF) protocol. This solves pain points around first-factor authentication because it is designed to replace the password, usually (but not exclusively) with a biometric factor that is retained only locally on the user device, never shared centrally or in the cloud. FIDO UAF is a strong authentication framework that enables online services and websites, whether on the open Internet or within enterprises, to transparently leverage native security features of end-user computing devices. In a FIDO ecosystem online service providers can easily achieve strong user authentication, and free users from creating and remembering more online credentials, simply by leveraging existing FIDO devices to authenticate at their sites and to use their services, such as mobile payments where UAF has seen early industry adoption.
If you are going to offer a replacement for passwords, you need a robust mechanism that isn’t based on the same “what you know” shared secret security design that has been the bane of password systems of late. We decided upon asymmetric public key cryptography, which uses a private key paired with a public key for each authenticator registration. However, we knew that putting the private key in the server could create vulnerability and undesired externalities in the case of a breach. We wanted to get to a model that would have no secrets on the server side. With FIDO authentication, the server holds a public key, but the private key is held only by the individual’s personal device, such as a mobile phone, and is never shared outside of that device. We saw the opportunity to make 1st factor authentication both easy & more secure by relying upon existing device-specific user verification methods being embedded in smartphones, tablets and PC’s. FIDO UAF then enables those local device authentication methods to be used securely online.
We found that before FIDO authentication, existing strong authentication options had very low user acceptance rates, sometimes less than 3% of users choosing to register for strong authentication when it was available as an option. The user acceptance of natural authentication methods that don’t tax the user’s memory or require extra steps in the process have been far more successful as seen by the increased number of people opting to lock their phone with gesture locks, 4 digit pin codes, and now biometric sensors like fingerprint sensors. However, under FIDO UAF, fingerprints are just one of many biometric options supported by the protocol- iris scanning, voice recognition, and behavioural sensors from wearable devices, are all supported in FIDO UAF.
We wanted a standard that could support any future authentication method, and support the industry in its drive to continuously innovate. Proprietary innovation happens between the device and user; this is where the industry can compete with differentiating solutions. FIDO standards come into play in the implementation between the device and the online service.
Another question is how online Payment Service Providers (PSPs) would know that the technique between device and user is trustworthy? FIDO standards incorporate the ability for online services like PSPs to set their own security policy defining the devices or device characteristics they want to trust. The members of the FIDO Alliance wanted a solution set that enabled trust between all devices and all services, but didn’t mandate it. They want a solution to be flexible enough to leave the trust decision in the hands of the online service provider who is in the position of making the risk decision related to any authenticated transaction.
We have discussed UAF in some detail. What then is U2F and where does it fit in the FIDO ecosystem?
FIDO U2F authentication addresses a totally different use case. FIDO UAF provides a simpler, stronger 1st factor authenticator where U2F provides a simpler, stronger 2nd factor authenticator. FIDO U2F does not replace the password but instead replaces the second factor and enables a simpler form of password, like a short PIN number, because the security burden can now be placed on the FIDO U2F authenticator and not the password. FIDO U2F has already been deployed by Google Accounts and now ships in all Google Chrome browsers.
So far the implementations of FIDO U2F authenticators are in the form of external specialized devices, but these capabilities could be embedded directly in handsets or other form factors in the future. What separates FIDO U2F security tokens from the OTP tokens discussed previously is that one device will work with any FIDO U2F server, regardless of vendor solution or device manufacturer. Another key differentiator is the phishing resistance inherent in the FIDO U2F standard. A FIDO U2F user cannot be tricked into giving a secret to a fraudster the way they can in a OTP use case.
Yubico and Plug-up are the two primary providers of U2F-enabled devices today, which work by being inserted into a USB slot. NFC and BLE support for U2F tokens is coming soon and will accommodate U2F devices for use with devices that don’t have USB slots.
To learn more about all the UAF and U2F FIDO Ready™ implementations please visit our website where they are all listed along with the profiles they support.
This is very interesting and thanks for helping to make our online experiences easier as well as more secure. Do you have any final message for us?
One thing I’d like to emphasize is the relationship between authentication and payments. Payments is just another application that requires strong user authentication. FIDO standards can be used for a whole variety of use cases that require strong online authentication… for healthcare applications, airline bookings, gaming, banking, enterprise use cases and anything that requires a user to authenticate online. The reason we saw the first adoption in mobile payments is because that industry segment had the greatest amount of pent-up demand for faster, easier strong authentication from mobile devices where typing passwords was the least convenient option.
The second topic I would like to emphasize is the relationship between FIDO standards and government regulation around strong authentication. Sticking with the payments example, you recently asked me about how FIDO UAF could be used to meet the criteria developed by regulatory regimes such as the EBA Guidelines. Though an analysis of exactly how a FIDO UAF implementation could meet the requirements of this specific regulation is beyond the scope of this interview, most multi-factor regulatory regimes are looking for two or more of a “what you know”, “what you are”, or “what you have” authentication factors. In just the example we see in the market already on Samsung Galaxy® devices, it may appear there is only a single “what you are” factor being offered by the fingerprint sensor, but there is also a “what you have” factor due to the secure protection of the private keys on the device, resulting in a multi-factor authentication event from a single user gesture. The Privacy and Public Policy Working Group in FIDO Alliance is going to make a concerted effort to educate regulators across various industries and geographical regions in 2015 to help them understand how to apply FIDO authentication to the markets they oversee.
Thanks Brett and I wish you the very best for all the further innovation that you plan in this very important space!
Brett McDowell currently serves as Executive Director of the Fast IDentity Online (FIDO) Alliance, the organization Brett helped establish in 2012 to remove the world's dependency on passwords through open standards for strong authentication. Brett is also an advisor to Agari and the Bitcoin Foundation.
Previously, Brett spent several years at PayPal where, as Head of Ecosystem Security, he was tasked with developing strategies and leading initiatives to make the Internet a safer environment for PayPal and their customers.
Author of The Digital Money Game, co-author Virtual Currencies – From Secrecy to Safety
http://www.linkedin.com/in/charmaineoak
Join me on Twitter @ShiftThoughtDM and The Digital Money Group on LinkedIn